95% of Cyberattacks Can Be Prevented—Follow These Website Security Tips to Protect Your Website From Hackers
From portable devices like smartphones, tablets, computers, laptops, or websites from small to big, all are vulnerable to cyberthreats. These days, ignoring cybersecurity is like keeping money on your house’s front porch and expecting to find it there once you return from vacation, which is quite impossible.
One famous example of cyberattacks is Yahoo. They announced that hackers had stolen 500 million users’ personal data. A further investigation of the data breach even revealed that 200 million customers’ data were for sale on a dark web marketplace.
Should I Worry About Getting Hacked?
According to research by Ponemon Institute, Verizon, and Forrester Consulting:
65+%
$34,604
40+%
30K+
But there’s one good side, though. In a recent Cyber Incident & Breach Trends Report by the Online Trust Alliance (OTA), researchers found that that 93% of cyber breaches are preventable. But for that, you need to take active steps by properly investing your time to make your site protected.
Top 21 Website Security Tips to Secure Your Site From Cyberattacks
Let’s go over some of the best website security tips to keep your site safe and secure from cyber crooks that will help to keep your data and brand reputation safe:
Securing Website Communication
Whenever anyone visits your website, sends an email, or uploads any file, communication occurs between their web browser and your website server. You’ll need to take a few steps to keep this communication safe.
1. Use HTTPS Connection Everywhere
One of the first website security tips you should implement in today’s world is to secure it with an HTTPS connection, which can be achieved using an SSL/TLS certificate provided by a respected certificate authority. The best certificate depends upon your website requirements – it differs from website to website. Due to Google’s policy, it’s mandatory to have an SSL/TLS certificate installed. Otherwise, your site visitors will see a warning message “Not Secure” or, at worse, the website will stop loading altogether on popular web browsers like Google Chrome or Mozilla Firefox.
Here’s How to Secure Your Website Using an HTTPS Connection
- Get an SSL/TLS certificate from a respected Certificate Authority (CA) like DigiCert, Sectigo, Thawte, or GeoTrust.
- Install your purchased SSL/TLS certificate through the control panel of your web hosting like cPanel.
- Update your CMS or website software to use HTTPS URLs by default instead of HTTP URLs.
- Update your site’s HTML code for referencing content like images to make use of HTTPS URLs.
- Make use of 301 redirects for pointing all HTTP URLs on your website to the secure HTTPS URLs.
Pro Tips About SSL/TLS Certificate
- Once you purchase an SSL certificate, it becomes your responsibility to take care of the private key. You’ll want to keep that private key safe. If hackers get your private keys, they can easily break the encryption and get your site’s valuable data.
- If your website has sensitive data from visitors like bank details or credit card details then an EV (Extended Validated) SSL certificate is the best to go with. It adds your company’s detail to the SSL certificate, giving visible clues to site users to ensure that they’re dealing with a safe website.
- Use tools like SSL Certificate checker and verify whether it’s installed correctly so users don’t face any warning messages while they visit your website.
- Make use of a CAA record to restrict which CAs can issue a certificate for your website. This gives better control and lets you decide who should issue SSL certificates for your site.
- Make use of HSTS (HTTP Strict Transport Security) that tells the browser to load website only through HTTPS. This is important for sites like banks or cryptocurrency websites with high chances of attacks such as MITM (Man-in-the-Middle) attacks.
- Make use of certificate monitoring and other management tools like CT log monitoring for tracking all SSL/TLS certificates used or issued for your site.
2. Make Use of FTPS or SFTP
As HTTPS is needed for opening a website safely, you should also make use of secure FTP for uploading or editing any website files. Two different versions are available: SFTP and FTPS. Both encrypt your passwords and other data while editing or uploading any file to the website.
Here’s How to Carry Out FTPS or SFTP Execution
- Most web hosting providers enable FTPS or SFTP, and you’ll simply need to get connection details for using it. Usually, they’re the same as the FTP connection details, but you’ll need to use a different port.
- It’s recommended that you verify the FTP server’s certificate details before connecting to the website server.
- Make sure that the FTP server you’re using uses an SSL certificate issued by a trusted certificate authority and not any self-signed certificate. Because certificates issued by CAs are trusted globally, and make it hard for an attack such as MITM that can impersonate your FTP server.
3. Encrypt Your Emails
First and foremost, it’s recommended not to share any critical information such as passwords, bank details, or any other sensitive things over email. But if you’ve got to do it, then be sure that you’re sending encrypted email. For instance, when you send login details through email, use end-to-end encryption to ensure that email doesn’t get intercepted or read by unauthorized parties or any cyber crook. There are two different ways to set up email encryption: S/MIME email encryption or sending email through a special encrypted email provider.
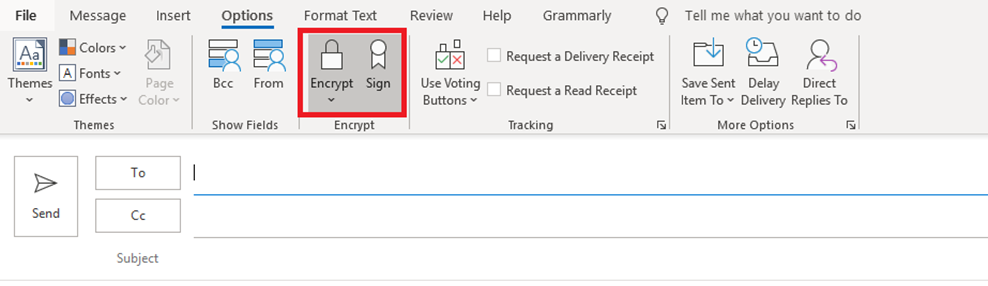
Click Encrypt For Sending Encrypted Email
- Both you and the person you’re sending an encrypted email to have an S/MIME certificate installed. If not, you can purchase a certificate through CAs (Certificate Authorities) like Sectigo.
- Once the email certificate is issued, you’ll need to install it into your email client, such as Outlook. For instance, in Outlook, you can install an email certificate by going to File > Options > Trust Center > Trust Center Settings > Email Security.
- Lastly, make sure that you’ve enabled the encryption option when composing an email.
Securing Website Access
Many hackers try attacking a website by breaking into the admin panel to gain complete access to the website. For instance, if the hacker gets their hands on a working admin username and password, they’ll be able to control your website and will be able to do their malicious deeds within seconds or minutes.
However, if you know how to secure your website against these attacks, you can implement defenses without any hassle that make it harder for hackers to log in to your website.
4. Keep Strong Passwords
You can count this under website security basics that don’t require spending a single dime. Make a habit of always using strong passwords.
Go through the below tips on how to keep strong and secure passwords:
- Long Passwords: The longer the password, the harder it is to guess because it increases the possible combinations during brute force attacks. If you make a slightly stronger password that’s not based upon a simple name or date of birth, then it can go a long way to make it dramatically stronger.
- Try Passphrases. The best way to create a password is through a passphrase that’s quite easy to remember for you but not easy for others to guess. If only you know the hidden meaning behind it it becomes hard to guess for everyone, even computers.
- Use Letters, Special Characters & Numbers: It’s also recommended that you choose a password that is longer and includes various special characters, upper-lower case letters, and numbers.
- Avoid Commonly Used Passwords: Most of the time, people tend to choose predictable passwords. When someone creates a password, there are high chances that they’ll create a password that is quite predictable and can be cracked easily. Also, there are high chances that they could use a password among those that are already hacked. You can find a list of some easily predictable passwords on this Wikipedia page that shows 10K commonly used passwords.
- Avoid Using the Same Passwords on Multiple Accounts: As the title implies, stop using the same passwords for multiple accounts where you’re providing any of your personal information. For example, don’t use the same password for two different shopping portals from where you order your stuff online, like using the same password for Amazon and eBay. It’s no brainer to say that same applies to other important accounts like banking websites. For instance, more than a billion Yahoo accounts were breached. So, if you’re using a password for any of your accounts that you’ve used for Yahoo, then there are high chances hackers already have your password.
- Avoid Passwords That Were Previously Breached on Other Sites: As mentioned above, hackers sometime get their hands on a previously breached database to use for new attacks. If you’re unsure whether your password has been involved in any previous data breach, you can verify online through HaveIBeenPwned.com.
- Avoid Easily Guessable Passwords: As the name implies, avoid those passwords that anyone can guess—for instance, your company name, pet name, or any commonly used dictionary words.
!LUvH!TT!NgDG!m$INCe!$TARTEd@18
! – I
LUv – Love
H!TT!Ng – Hitting
D – The
G!m – Gym
$INCe – Since
! – I
$TARTEd – Started
@ – At
18 – Age 18 years
5. Minimize Repeated Login Attempts
This is the simplest, effective defense mechanism against brute force attacks that happen on websites. Simply block visitors who try login into the website multiple times by entering incorrect passwords.
Here’s How to Implement Login Restrictions
- If you’re using a popular CMS such as WordPress, you can easily get plugins that help to block repeated login attempts.
- If you’ve custom coded your website, then popular programming frameworks have built-in features that enable login lockouts due to incorrect passwords.
6. Apply MFA (Multi-Factor Authentication)
If any hacker finds your admin password via phishing or malware attack, there’s one more way to prevent them from getting into the website. It’s through multi-factor authentication, often called 2-factor authentication.
- Mutual authentication through digital certificates
- OTP (One-time passwords/verification codes) sent through email or SMS
- Verification is completed through a token.
- Verification through a mobile app like Google Authenticator
Here’s How to Apply 2FA/MFA
- For certificate-based multi-factor authentication, you’ll need to purchase a personal authentication certificate for all the admin users and configure it on your web server and web application to restrict admin access to permitted users.
- SMS-based 2FA is quite easy and can be done using different services and plugins available. For instance, WordPress offers several plugins that can enable MFA.
7. Separate Accounts & Permissions
A good way to keep your site secure by reducing risk is by limiting every person’s access to the website according to their role. This way, even if a hacker gets their hands on their account, they will get only limited access and not be able to damage the entire website.
For Correct Access, Make Sure That:
- Every user has access to the website through their own username and password.
- Avoid sharing an account.
- Grant the permissions needed for the job role and nothing more.
All You Need to Do Is:
- Regularly review all accounts along with their permissions on your website.
- If multiple users use any account, it’s recommended to delete the account and create separate accounts per user.
- If any account has access to a certain part that’s not needed according to their job profile, remove those permissions and keep the access limited according to their role.
8. Remove / Delete Old Accounts
Just like it’s recommended to limit permissions on each account, it’s also recommended that you should delete old accounts that are not used by anyone. If a hacker gets access to old account details, they’ll be able to log in and do their evil deeds through an account which wasn’t even needed in the first place.
Some Tips for Implementing This Website Security Tip
Whenever any employee or contractor leaves the company, it’s best to review its access permission and update the password or remove accounts specifically given to them.
- At least once a month, review all the accounts and permissions.
- You’ll likely find an account that can be removed or restricted with minimum rights.
Securing Emails
Emails are one of the most critical communication channels for most organizations and businesses, where plans are hatched, critical information is shared, and alliances are formed. Yet, it’s an insecure medium, and emails are often considered one of the ‘weakest links’ within an organization’s security strategy and policies. Indeed, more than 90% of cyber-threats originate within the email environment.
Here are some common ways to avoid email-based attacks and phishing emails:
9. Setting Spam Filters
One in every 99 emails is a phishing attack, and the best way to fight such email threats is by using spam filters to block the scam email before it reaches its destination. The best spam and malware filters can block more than 90% of those harmful and malicious emails before reaching the recipient’s inbox.
Features to Look for in a Spam Filter
- It should be based upon real-time spam intelligence that includes spam blacklists.
- Respects record settings like SPF and DKIM.
- It offers an advanced malware scanner that doesn’t rely upon fingerprinting files (because malware changes quickly).
- Allows users to add email senders to a blacklist or whitelist.
- Allows admins to add senders to a blacklist or whitelist.
10. Provide Anti-phishing Training
Similar to other cyber-attacks, a phishing attack also focuses on human weaknesses. It’s not an attack against technology, but it’s a scam that dupes users using malicious tactics. Even with advancing technology, phishing is not going to stop completely, but users have to start focusing on protecting themselves and not becoming victims of such attacks.
Users should go through anti-phishing training– an effective defense against phishing attacks that helps employees learn how to detect and handle malicious phishing emails.
11. SPF, DKIM, DMARC Protocols for Preventing Spammers
- SPF – Sender Policy Framework
- DKIM – DomainKeys Identified Mail
- DMARC – Domain-based Message Authentication
Here’s how:
- SPF lets you specify servers that should be allowed for sending emails from your domain.
- DKIM lets you specify who should be allowed to send emails through your domain.
- DMARC works as a reporting system that tracks if any non-authorized sender has tried sending email through your domain.
Deployment of Pro-active Website Defense Systems
Building your website with robust coding and proper database security to prevent commonly known attacks is the first step for any secured website, but it doesn’t stop there. Other security steps are needed to prevent attacks that can happen even if the website is securely coded. Here are a few website security tips to help you setup defense systems for your site:
12. Setting Up Vulnerability Scanning
Vulnerabilities in the website are weaknesses that hackers look for and use to attack the site. For overcoming this issue, one of the easiest ways is to do vulnerability scanning using a scanner like HackerGurardian PCI Scanning. It’s a security tool offered by Sectigo which automatically reviews website code and other possible vulnerabilities so you can fix it before a hacker finds and exploits it.
Here are a few tips when looking for a vulnerability scanner:
- Choose a vulnerability scanner whose database is regularly updated for known vulnerabilities.
- Choose scanners that check your CMS (Content Management System). For instance, if you’re using WordPress, then ensure your vulnerability scanner does full scanning of installed themes, plugins, and the core of your CMS.
- Get a scanner that can rate and provide details of every vulnerability so you can know on your own how severe it is, whether it has to be fixed or it’s okay to overlook, at what priority it should be fixed, and how you can find the solution.
- Ensure that it allows you to setup automated scanning through email alerts for all found vulnerabilities so you can stay alerted as soon as an issue is found.
13. Setting Up Malware Scanner
You may be thinking, is it necessary to have a malware scanner? Won’t everyone find out if the website is infected or hacked? It may sound strange, but many times hacked or malware-infected sites go unnoticed for awhile, and a whole lot of damage is done before anyone figures it out. For example, sending spam messages, stealing important data, linking to malicious websites, etc.
Tactics used by hackers that makes them go unnoticed include:
- Displaying a normal website to most users.
- Adding webpages that remain hidden. So, no one can figure out while surfing the site normally.
- Detecting the site visitor’s country and displaying the hacked website to certain country visitors.
- In Google Search, displaying hacked or altered pages.
Tips on Selecting a Malware Scanner
- Choose a malware scanner that doesn’t rely upon fingerprinting files to identify malware-savvy hackers who insert their malware into legitimate website files that are hard to find.
- Ensure the malware scanner you choose offers detailed information on the identified malware, such as which file is infected by it, the file type/name, etc.
- Be sure that your chosen malware scanner is capable enough to detect malware that’s injected into the database.
- Choose one that provides features that can find and remove malware if website gets hacked.
14. Deploying a WAF (Web Application Firewall)
A WAF (Web Application Firewall) is a proven method for securing your website by preventing attacks before they even reach your site. In other words, a WAF is between the website and the internet to check the requests of every visitor and reject all of the malicious ones based upon a pre-set list of rules.
An effective WAF (Website Application Firewall) is based upon rules that have to effectively detect and prevent any possible attack like SQL injection and other new vulnerabilities.
Some WAFs are quite complex, expensive pieces of software that may run on a dedicated hardware device at the enterprise level. On the other hand, small businesses that don’t have a big budget or personnel for implementing and managing a big, complex Enterprise WAF that comes with expensive software and require dedicated hardware devices can still setup effective WAF. The main options are like going for a server-level WAF including in your web hosting package, a server-level WAF that can be managed on your own, and a cloud-based WAF that runs on a CDN (Content Distribution Network).
Secure Code & Database
While building your website, the code and database should be built to resist common attacks. To achieve security for your database and code, some of the things you should follow are:
15. Hash Your Passwords
Password hashing is a basic tactic that every developer should apply. Before storing passwords directly into the database, hashing is a mandatory step. For instance, if hackers get their way into the database, they would get all their passwords of every stored account if they’re not hashed.
Hashing is the technique that converts any given password into a string of random characters. For instance:
If we have a password: Web$ec$tore@) then the hashed password using SHA-256 algorithm will be:
- If you’re using the same text and same algorithm, it’ll provide the same hash value every time you convert.
- Hashing is one-way, so it can’t be decrypted or reversed back to the original text value once it gets hashed.
16. Encrypt Sensitive Information in the Database
As discussed, a password should be stored in hash-values. Similarly, other information like credit card numbers, Tax IDs, and other sensitive data should be stored in the database in an encrypted format. This helps to ensure that only you’re allowed to use the data, not hackers, and even if they get their hands on it, it remains useless for them due because it’ll be ciphertext.
17. Keep Software Updated
Keep all installed software updated. This is critical because hackers love to abuse security holes. Software updates are important for both software you’ve installed on your sites (such as CMS or forum) and server software (such as the operating system).
If you’ve installed third-party software on your sites like a CMS or forum, you should make sure that you update with the patch at the earliest possible date when available. Many vendors have a mailing list or RSS feed that sends out information about an issue pertaining to web security. Moreover, CMSes like WordPress or Umbraco notifies you regarding system updates once you log in.
18. Use Secured Libraries & Frameworks
The best part about using libraries and frameworks during the website development phase is that good libraries and frameworks include powerful security features. Different types of security features come equipped either by default or available as a feature within programming frameworks.
For instance, here is a list of key security features that come in two of respected coding frameworks:
| Security Features | Laravel | ASP.NET |
|---|---|---|
| Encryption | Included | Included |
| Hashing Passwords | Includes Hash | Included as PBKDF2 feature |
| XSS Protection | Included | Included as an Add-on called AntiXSS |
| Always-On HTTPS | Various Options Are Available | Included within Web.config file |
| Brute Force Protection | Included within LoginController | Provided as Add-on: AllowXRequestsEveryXSecondsAttribute |
| Preventing SQL Injection | Offered as Fluent Query Builder or Eloquent | Offered as Entity Framework |
| Security Enforcement For Minimum Password | Requires Add-on | Included (Identity) |
19. Use Best Practices of Secure Coding
It’s suggested that you follow well-established security practices that address major issues of potential security problems. For instance, OWASP (Open Web Application Security Project) publishes guides and cheat sheet for many popular programming languages such as:
- Ruby on Rails (RoR)
- Nodejs
- HTML5
- REST
- DotNet
- AJAX
20. Consider Static Website
If your website is a simple website that doesn’t need dynamic features, consider creating a static website using HTML instead of a CMS such as WordPress. You can still use a user-friendly editor and just export the finished site code.
If your website requires using a few dynamic features, you’ll be able to do so using a static website with third-party widgets that offer dynamic features. Some of the popular widgets that you can use for adding dynamic features for static websites include:
- Blog Commenting: Facebook or Disqus Commenting plugin
- Contact Forms: Typeform, JotForm,Formstack, Zoho Forms, or Google Forms.
- Site Search: AddSearch, FreeFind, Swiftype
21. Regular Backups
It doesn’t matter how secure your website is. It’s best to practice regular backups of your website. Backups must be kept as a critical part of your website protection strategy because it’s quite certain that something will go wrong sooner or later.
If you get in the habit of making backups regularly, it can help you restore your website to working condition if anything goes wrong. It’s best practice to automate your backups and keep them separately from your site or website hosting account.
Wrapping Up
Now you know how to secure your website using proven website security tips that work for any type of site. Many websites from small to big get attacked by cybercriminals daily, and it shouldn’t come as a surprise that cyber-attacks are becoming more common with every passing year. In other words, you should have website security plans that help mitigating attacks like malware, DDoS, phishing emails, and SQL injection.
In this article we’ve covered some of the best website security tips that will help you secure your site from such commonly seen attacks while keeping yourself protected. What are your favorite tips for securing your website? Share them in the comments!